I upgraded to a newer work phone on the same platform and assumed everything would “just show up.” It mostly did—until I realized a few local folders and an authenticator setup didn’t come across, and I’d already started the return process.
Forum user
A same-platform work phone upgrade (Android→Android or iPhone→iPhone) often fails for one simple reason: the transfer isn’t the risky part—the missed verification step is.
This guide gives you AI planning prompts to build a sequenced, evidence-based workflow (inventory → transfer → verify), then shows how to execute that workflow safely with real device-to-device transfer actions.

In this article
- Plan a same-platform work phone upgrade without missing critical steps
- Why “same ecosystem” still misses data
- Quick summary checklist
- The irreversible “point of no return”
- What AI can’t do for you
- What the AI needs to know
- AI prompts to build a safer workflow
- AI plan vs. real device constraints
- When to stop planning and start execution
Part 1. Plan a same-platform work phone upgrade without missing critical steps
You’re upgrading a company phone to a newer model on the same platform (Android→Android or iPhone→iPhone). You expect your documents, photos, messages, work apps, and settings to appear exactly the same—because it’s “the same ecosystem.”
But one missed toggle, account sync gap, or work-profile restriction can leave you without a folder, thread, or app data you assumed was included. The biggest risk is usually not the transfer itself, but skipping a verification step you can’t redo later.
1-1. Why “same ecosystem” still misses data
After asking AI, you may get a general checklist, but still feel uncertain about sequence: do you sign into the new phone first, or back up first? Do you move the SIM before verifying MFA? Which items won’t migrate (authenticator tokens, app-specific encrypted data, work-profile data)?
1-2. Quick summary checklist
1. Write the sequence before you touch anything irreversible.
Split the workflow into preparation, execution, and verification, and add “stop” gates before wiping, trade-in, or returning the old phone.
2. Inventory what must transfer and define proof.
Use evidence you can verify (photo counts, named folders like Downloads/WorkDocs, key chats, and work access like MFA/VPN/email) instead of guessing.
3. Treat work controls and app encryption as high risk.
Work profiles/MDM, authenticator tokens, and encrypted chat histories may not transfer automatically; plan app-specific mitigation steps.
1-3. The irreversible “point of no return”
There’s a point of no return: factory resetting, wiping, trading in, or handing back the old phone. If that happens before you verify critical files and access, you may permanently lose data or lock yourself out of work systems.
1-4. What AI can’t do for you
AI helps by turning “move everything to my new phone” into a sequenced workflow: what to inventory, what to back up, what to verify, and what to treat as high-risk or non-transferable (work profiles, MFA apps, encrypted chats, device-managed restrictions).
But AI can’t actually connect to your phones, read your storage, or perform device actions. Once the plan is validated, you’ll still need real execution tools and your organization’s approved policies to complete the transfer safely.
Part 2. What the AI needs to know
Share your situation so the AI can produce a workflow that matches your constraints and risk level.
- Platform and models (e.g., “iPhone 12 → iPhone 15” or “Pixel 6 → Pixel 9”)
- Ownership/management (personal device, BYOD, company-owned, MDM/Intune, work profile)
- Data types that must not be missed (local files, photos, messages, call logs, WhatsApp/Signal, notes, voice memos, downloads)
- Work-critical access dependencies (MFA app, hardware keys, VPN, certificates, email profiles)
- Storage constraints (old phone storage used, new phone storage free, computer available)
- Allowed tools and policies (whether cloud backup is permitted, whether USB transfers are allowed)
- Deadline and downtime tolerance (minutes vs hours, business hours only, travel)
- “Do not lose” list (top 10 folders/apps/chats that must be verified before wipe)
Part 3. AI prompts to build a safer workflow
Use the prompts below to force a clear sequence, reduce guesswork, and define verifications before you touch anything irreversible.
3-1. Level 1: Basic prompt
I’m upgrading a work phone to a new phone on the same platform and I can’t miss any files.
Create a step-by-step plan with a short verification checklist after each major step.
Include common items that do not transfer automatically.
3-2. Level 2: Advanced prompt
Build me a structured workflow for a same-platform work phone upgrade that minimizes the chance of missing files.
Separate it into Preparation / Execution / Verification, and label each step as Critical or Optional.
Call out high-risk moments I must not do until verification is complete (like wiping, trade-in, or removing accounts).
3-3. Level 3: Evidence prompt
Here’s my context: platform upgrade (iPhone 12 → iPhone 15), company-managed email + VPN, MFA app in use, and I must not lose local files in Downloads and a few app folders.
I have a laptop available and a USB cable, and I can tolerate 2 hours downtime.
Create a workflow with checks before/during/after execution, including:
- an inventory list I should capture (e.g., “Top 10 folders: Downloads/WorkDocs (2.4 GB), Photos (18,000), Notes (350)”)
- a “must-verify” list for work access (e.g., “MFA works, VPN connects, email syncs, calendar updates”)
- explicit stop conditions that prevent me from wiping the old phone until evidence is confirmed.
3-4. Prompt refinement (follow-up prompts)
Rewrite the plan as a single-page runbook with: inputs, prerequisites, steps, verification evidence, and rollback options.
Create a verification matrix with columns: Data type → Where it lives → Transfer method → How to confirm → Pass/fail evidence.
Identify which items are likely not transferable (authenticator tokens, encrypted chats, app sandboxes) and propose safe mitigations for each.
Ask me 10 clarifying questions, then output a final plan that includes a “do not proceed if…” gate before any wipe/trade-in action.
Convert the workflow into a timeboxed schedule (e.g., T-60 min prep, T+0 execution start, T+90 verification) with dependencies.
Part 4. AI plan vs. real device constraints
AI improves planning, but cannot execute. It can’t connect cables, authenticate accounts, move data, or confirm what actually transferred—your tools and checks must do that.
| Planning with AI | Real constraint on devices |
|---|---|
| Produces a complete sequence with risk gates | Devices may block actions due to MDM, encryption, or policy |
| Generates verification checklists and evidence criteria | You must manually confirm data presence and app access |
| Flags non-transferable items and mitigation options | Some apps/data can only be restored via that app’s own backup/login |
| Creates rollback/hold rules before irreversible steps | Only real tools and device settings can execute transfer/backup |
Part 5. When to stop planning and start execution
Once you meet the conditions below, planning is no longer the bottleneck—execution and evidence collection are.
- You have a written sequence with Critical steps and clear “stop” gates before any wipe/trade-in.
- You have an inventory of what must transfer (folders, apps, chats, work access) and how you’ll verify each.
- You’ve confirmed constraints (MDM policy, storage space, cables/computer availability, time window).
- You’ve defined the irreversible moment: the old phone is not wiped, reset, traded in, or returned until verification passes.
5-1. Execute the workflow safely with a real transfer tool
Execution now matters because this is where mistakes become permanent: skipping a backup, selecting the wrong data category, overwriting existing data, or proceeding to wipe before confirming results.
-
Step 1 Pre-transfer baseline capture
Before you move anything, write down what “complete” means for your job (your “must-not-miss” list), and ensure both phones are available, powered, and unlocked as required.
-
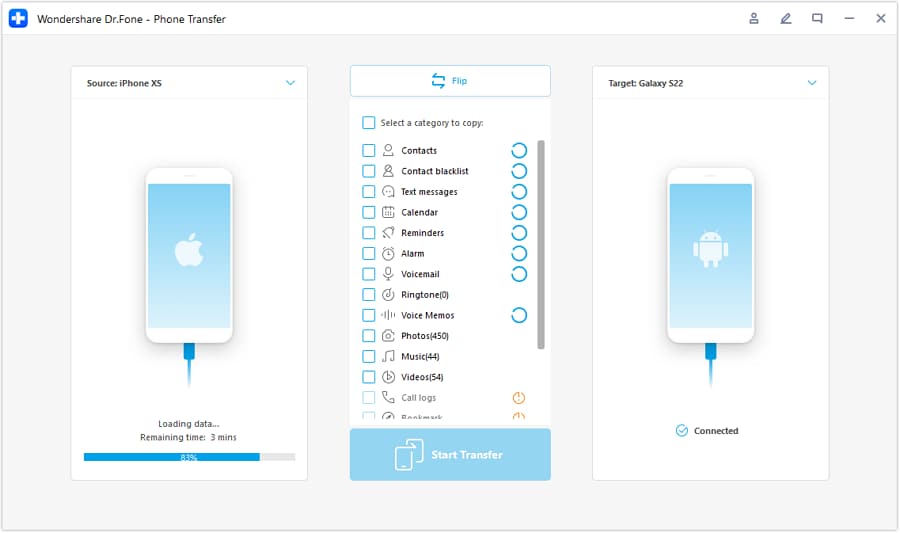
Step 2 Set the correct source/target path
Start the device-to-device transfer workflow and confirm you’re moving from the old phone (source) to the new phone (target). If the direction is wrong, your result may be incomplete or overwrite data you meant to keep.
-
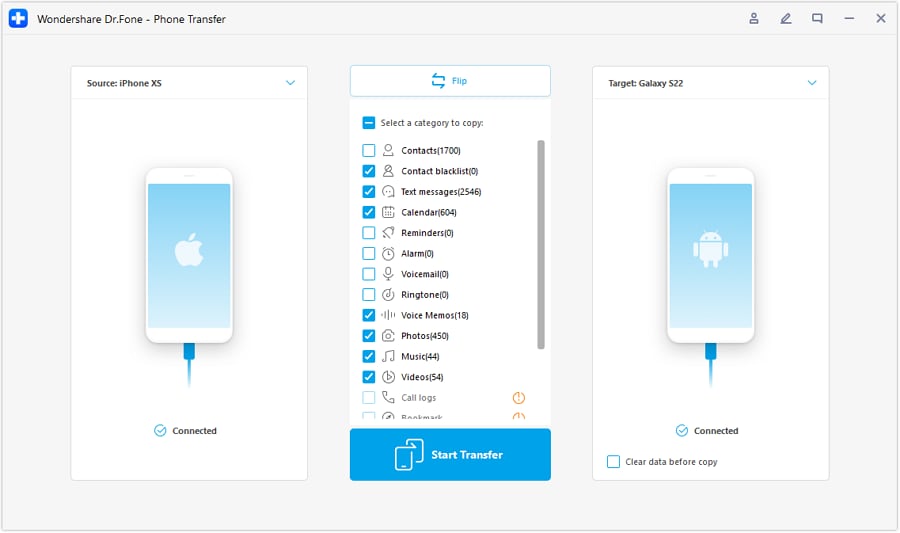
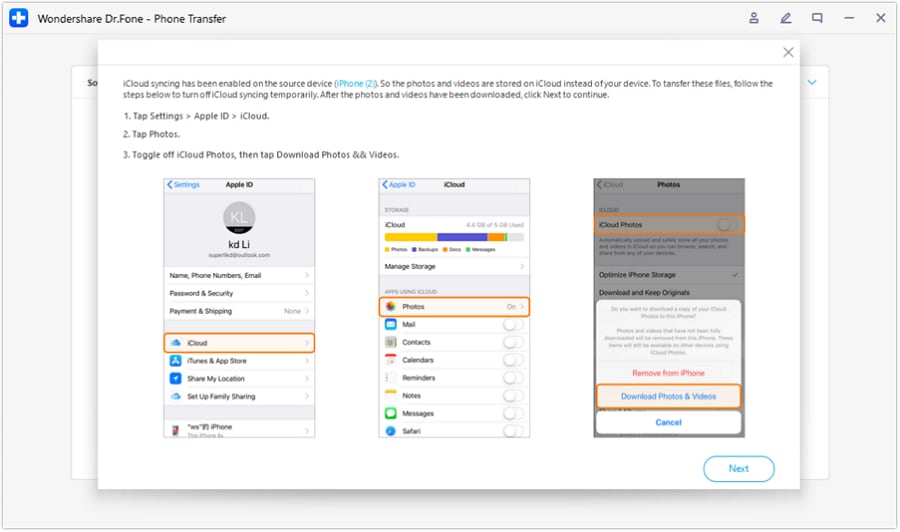
Step 3 Choose data categories carefully
Select the data categories that match your plan (files/folders, photos, messages, and any work-critical data you’re allowed to transfer). Don’t assume “everything” is included—verify category-by-category.
-
Step 4 Controlled completion and verification before any wipe
Do not interrupt cables/power or skip required on-screen approvals. After completion, verify your “must-not-miss” evidence on the new phone (folder names and files, photo counts, key conversations, MFA/VPN/email access) and keep the old phone intact until all critical checks pass.
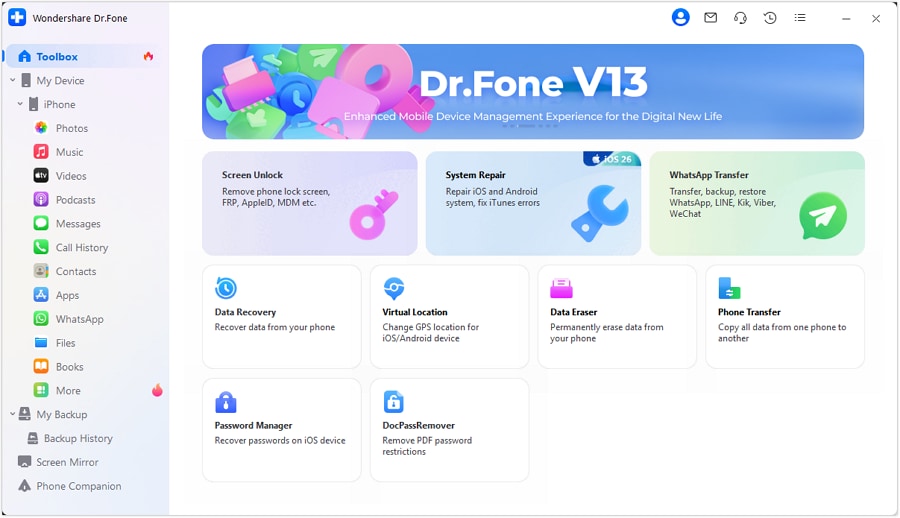
Recommended tool for executing your upgrade plan
After AI helps you design a sequenced runbook with verification gates, use Dr.Fone - Phone Transfer to perform the real device-to-device transfer actions—then validate the results with your evidence checklist before any wipe, trade-in, or return.
To keep the process safe in a work context, treat the transfer tool as “execution,” and your checklist as “proof.” If you can’t prove a critical item transferred (local folders, key chats, MFA/VPN/email access), do not proceed to wiping or returning the old device.
Conclusion
Use AI to design a sequenced workflow with risk gates and verification evidence, then use Dr.Fone to perform the real transfer and backup actions—without crossing the irreversible wipe/trade-in moment until your checks are complete.
FAQ
-
What’s most commonly missed in same-platform upgrades?
Authenticator/MFA tokens, app-specific local files, encrypted chat histories, work-profile data under MDM, and “Downloads” or offline folders that weren’t included in the chosen transfer path.
-
When is the “point of no return”?
Factory reset, wipe, trade-in, returning the device to IT, or removing key accounts/security profiles from the old phone—do not do any of these until verification passes.
-
How do I verify “everything transferred” without guessing?
Use a short evidence list: counts (photos/videos), named folders (Downloads/WorkDocs), key conversations, and logins (MFA, VPN, email). If you can’t prove it, treat it as not transferred.
-
Can AI tell me what’s on my old phone or confirm the transfer succeeded?
No. AI can only propose a checklist and sequence; it cannot access your storage, app sandboxes, or transfer logs unless you provide screenshots/outputs.
-
Should I sign into work accounts on the new phone before or after transfer?
Follow your org policy and your plan’s dependency order. If work access depends on MFA on the old device, prioritize preserving that access path until the new device is confirmed working.
-
How long should I keep the old phone after the upgrade?
Until all critical verification is complete and stable (often 24–72 hours, depending on policy), and only then proceed with wipe/trade-in/return.













 100% Security Verified | No Subscription Required | No Malware
100% Security Verified | No Subscription Required | No Malware

 :
: 
 ChatGPT
ChatGPT
 Perplexity
Perplexity
 Gemini
Gemini
 Claude
Claude
 Grok
Grok

 Move data between iOS to Android and vice versa.
Move data between iOS to Android and vice versa.




 Add Wondershare Dr.Fone as a preferred source on Google
Add Wondershare Dr.Fone as a preferred source on Google